This powershell module is built to be used with Bernie White's excellent PSRule module to check an Azure DevOps project for best practices for a secure development environment. The module takes best practices from the official Azure DevOps Security best practices documentation. It can function as a periodic security scan and check for your Azure DevOps project.
This module is actively developed since August 2023. Although a lot of testing has been performed and is built in to the development cycle, up to now little feedback has come back from the community yet. Any input on the direction of the module and included rules is very much appreciated. Please consider opening an issue with your ideas, encountered problems in using the module or other contributions. Any feedback is highly appreciated.
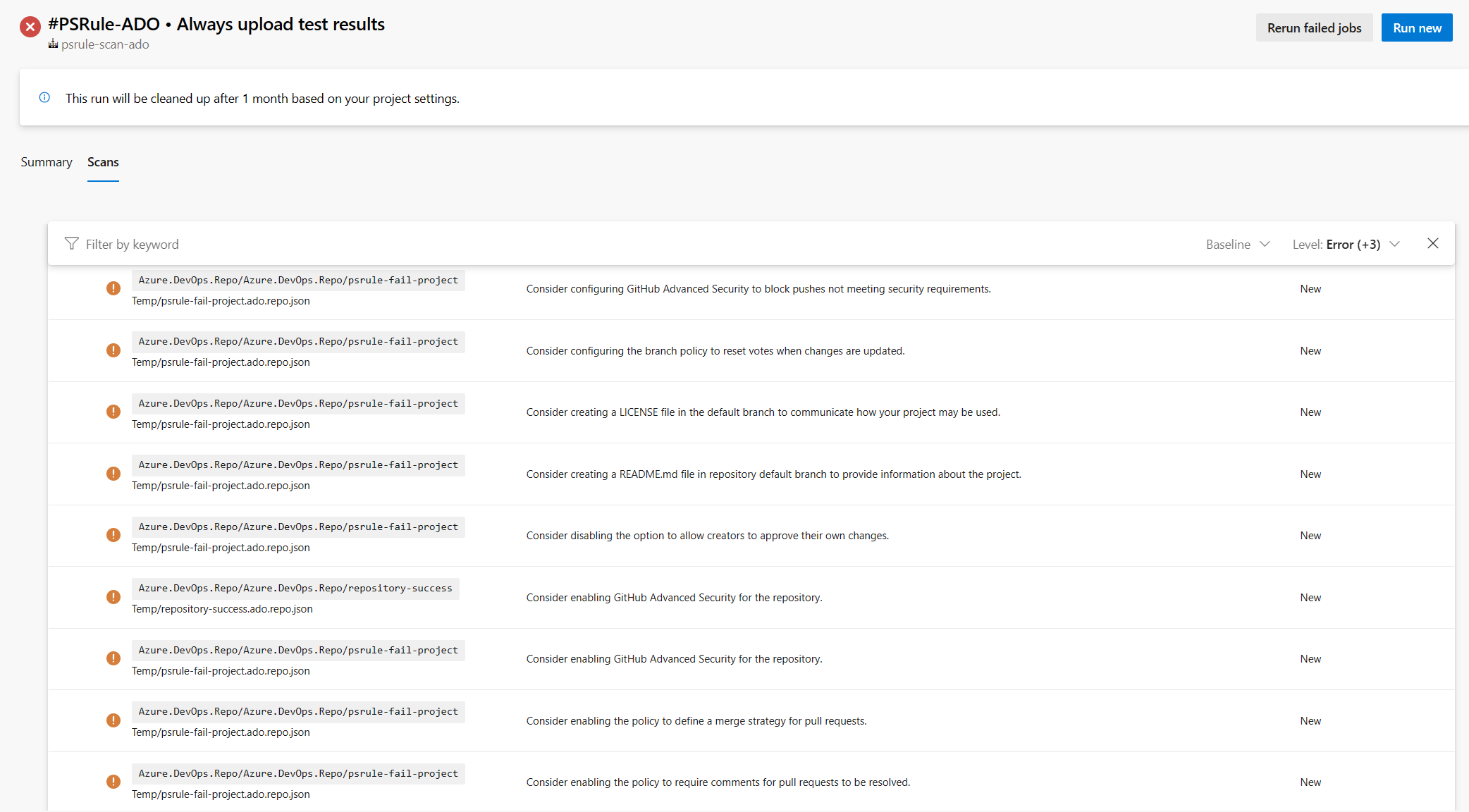
If you are looking for an easy to use spin-off project that uses this module and gives you a nice dashboard in Azure Monitor, please have a look at the PsrAzDo-workbooks project. It is a set of Azure Monitor Workbooks that can be used to visualize the results of the PSRule.Rules.AzureDevOps module. The workbooks are easily deployed through through the included Bicep template and modules. A Yaml pipeline is included to run the PSRule.Rules.AzureDevOps module on a daily basis and upload the results to Azure Monitor.
To use this module, you need to have PSRule installed. You can install it from the PowerShell Gallery:
Install-Module -Name PSRule -Scope CurrentUserOnce you have PSRule installed, you can install this module from the PowerShell Gallery:
Install-Module -Name PSRule.Rules.AzureDevOps -Scope CurrentUserOnce you have both modules installed, you can connect to your
Azure DevOps organization and run an export of your Azure DevOps
project and run the rules on the exported data.
The -PAT value needs to be an Azure DevOps Personal Access Token
with sufficient permissions to read the project data. The default
expects a PAT with full access permissions. Alternately, you can
use a PAT with only read permissions or fine-grained permissions
with the -TokenType parameter. The fine-grained permissions expect
read access to all scopes and read & manage for scope that do not
have read-only access. Documentation on how to create the PATs can
be found in the docs/token-permissions.md.
Connect-AzDevOps `
-Organization "MyOrg" `
-PAT $MyPAT
Export-AzDevOpsRuleData `
-Project "MyProject" `
-OutputPath "C:\Temp\MyProject"
Assert-PSRule `
-InputPath "C:\Temp\MyProject\" `
-Module PSRule.Rules.AzureDevOpsConnect-AzDevOps `
-Organization "MyOrg" `
-PAT $MyPAT `
-TokenType ReadOnly
Export-AzDevOpsRuleData `
-Project "MyProject" `
-OutputPath "C:\Temp\MyProject"
Assert-PSRule `
-InputPath "C:\Temp\MyProject\" `
-Module PSRule.Rules.AzureDevOpsSince version 0.3.0 of this module, you can also connect to your
Azure DevOps organization with a Service Principal or Managed Identity.
The -AuthType parameter can be set to ServicePrincipal or ManagedIdentity.
The Service Principal needs to have sufficient permissions to read the
project data. The default expects a Service Principal with project
administrator permissions. Alternately, you can use a Service Principal
with only read permissions or fine-grained permissions with the -TokenType
parameter.
Connect-AzDevOps `
-Organization "MyOrg" `
-AuthType ServicePrincipal `
-ClientId $MyAppId `
-ClientSecret $MyAppSecret `
-TenantId $MyTenantId
Export-AzDevOpsRuleData `
-Project "MyProject" `
-OutputPath "C:\Temp\MyProject"
Assert-PSRule `
-InputPath "C:\Temp\MyProject\" `
-Module PSRule.Rules.AzureDevOpsConnect-AzDevOps `
-Organization "MyOrg" `
-AuthType ManagedIdentity
Export-AzDevOpsRuleData `
-Project "MyProject" `
-OutputPath "C:\Temp\MyProject"
Assert-PSRule `
-InputPath "C:\Temp\MyProject\" `
-Module PSRule.Rules.AzureDevOps$env:ADO_MSI_CLIENT_ID = $MyClientId
Connect-AzDevOps `
-Organization "MyOrg" `
-AuthType ManagedIdentity `
Export-AzDevOpsRuleData `
-Project "MyProject" `
-OutputPath "C:\Temp\MyProject"
Assert-PSRule `
-InputPath "C:\Temp\MyProject\" `
-Module PSRule.Rules.AzureDevOpsSince version 0.0.8 of this module, you can also export the data at the organization level, looping through all projects in the organization the PAT has access to.
Export-AzDevOpsOrganizationRuleData `
-OutputPath "C:\Temp\MyOrg"Since version 0.0.12 of this module, you can disable rules that
check for Azure DevOps features that require additional licenses.
This is done through applying the Baseline.NoExtraLicense
baseline to the Assert-PSRule command through the -Baseline
option.
Assert-PSRule `
-InputPath "C:\Temp\MyProject\" `
-Module PSRule.Rules.AzureDevOps `
-Baseline Baseline.NoExtraLicenseDocumentation for the implemented rules can be found in the en folder in the module folder.
This annotated version of the official security best practices provides a reference for how the rules in this module are related to the best practices recommended by Microsoft. It is the main guiding document in building the ruleset for this module.
- Azure.DevOps.Groups.ProjectAdmins.MaxMembers
- Azure.DevOps.Groups.ProjectAdmins.MinMembers
- Azure.DevOps.Groups.ProjectValidUsers.DoNotAssignMemberOfOtherGroups
- Azure.DevOps.Pipelines.Core.InheritedPermissions
- Azure.DevOps.Pipelines.Core.NoPlainTextSecrets
- Azure.DevOps.Pipelines.Core.ProjectValidUsers
- Azure.DevOps.Pipelines.Core.UseYamlDefinition
- Azure.DevOps.Pipelines.Environments.Description
- Azure.DevOps.Pipelines.Environments.InheritedPermissions
- Azure.DevOps.Pipelines.Environments.ProductionBranchLimit
- Azure.DevOps.Pipelines.Environments.ProductionCheckProtection
- Azure.DevOps.Pipelines.Environments.ProductionHumanApproval
- Azure.DevOps.Pipelines.Environments.ProjectValidUsers
- Azure.DevOps.Pipelines.PipelineYaml.AgentPoolVersionNotLatest
- Azure.DevOps.Pipelines.PipelineYaml.StepDisplayName
- Azure.DevOps.Pipelines.Releases.Definition.InheritedPermissions
- Azure.DevOps.Pipelines.Releases.Definition.NoPlainTextSecrets
- Azure.DevOps.Pipelines.Releases.Definition.ProductionApproval
- Azure.DevOps.Pipelines.Releases.Definition.ProjectValidUsers
- Azure.DevOps.Pipelines.Releases.Definition.SelfApproval
- Azure.DevOps.Pipelines.Settings.LimitJobAuthorizationScope
- Azure.DevOps.Pipelines.Settings.LimitJobAuthorizationScopeForReleasePipelines
- Azure.DevOps.Pipelines.Settings.LimitJobAuthorizationScopeForYamlPipelines
- Azure.DevOps.Pipelines.Settings.LimitSetVariablesAtQueueTime
- Azure.DevOps.Pipelines.Settings.RequireCommentForPullRequestFromFork
- Azure.DevOps.Pipelines.Settings.RestrictSecretsForPullRequestFromFork
- Azure.DevOps.Pipelines.Settings.SanitizeShellTaskArguments
- Azure.DevOps.Pipelines.Settings.StatusBadgesPrivate
- Azure.DevOps.Project.MainEnvironmentAcl.ProjectValidUsers
- Azure.DevOps.Project.MainPipelineAcl.ProjectValidUsers
- Azure.DevOps.Project.MainReleaseDefinitionAcl.ProjectValidUsers
- Azure.DevOps.Project.MainRepositoryAcl.ProjectValidUsers
- Azure.DevOps.Project.MainServiceConnectionAcl.ProjectValidUsers
- Azure.DevOps.Project.MainVariableGroupAcl.ProjectValidUsers
- Azure.DevOps.Project.Visibility
- Azure.DevOps.Repos.Branch.BranchPolicyAllowSelfApproval
- Azure.DevOps.Repos.Branch.BranchPolicyCommentResolution
- Azure.DevOps.Repos.Branch.BranchPolicyEnforceLinkedWorkItems
- Azure.DevOps.Repos.Branch.BranchPolicyIsEnabled
- Azure.DevOps.Repos.Branch.BranchPolicyMergeStrategy
- Azure.DevOps.Repos.Branch.BranchPolicyMinimumReviewers
- Azure.DevOps.Repos.Branch.BranchPolicyRequireBuild
- Azure.DevOps.Repos.Branch.BranchPolicyResetVotes
- Azure.DevOps.Repos.Branch.HasBranchPolicy
- Azure.DevOps.Repos.DefaultBranchPolicyAllowSelfApproval
- Azure.DevOps.Repos.DefaultBranchPolicyCommentResolution
- Azure.DevOps.Repos.DefaultBranchPolicyEnforceLinkedWorkItems
- Azure.DevOps.Repos.DefaultBranchPolicyIsEnabled
- Azure.DevOps.Repos.DefaultBranchPolicyMergeStrategy
- Azure.DevOps.Repos.DefaultBranchPolicyMinimumReviewers
- Azure.DevOps.Repos.DefaultBranchPolicyRequireBuild
- Azure.DevOps.Repos.DefaultBranchPolicyResetVotes
- Azure.DevOps.Repos.GitHubAdvancedSecurityBlockPushes
- Azure.DevOps.Repos.GitHubAdvancedSecurityEnabled
- Azure.DevOps.Repos.HasDefaultBranchPolicy
- Azure.DevOps.Repos.InheritedPermissions
- Azure.DevOps.Repos.License
- Azure.DevOps.Repos.ProjectValidUsers
- Azure.DevOps.Repos.Readme
- Azure.DevOps.RetentionSettings.ArtifactMinimumRetentionDays
- Azure.DevOps.RetentionSettings.PullRequestRunsMinimumRetentionDays
- Azure.DevOps.ServiceConnections.ClassicAzure
- Azure.DevOps.ServiceConnections.Description
- Azure.DevOps.ServiceConnections.GitHubPAT
- Azure.DevOps.ServiceConnections.InheritedPermissions
- Azure.DevOps.ServiceConnections.ProductionBranchLimit
- Azure.DevOps.ServiceConnections.ProductionCheckProtection
- Azure.DevOps.ServiceConnections.ProductionHumanApproval
- Azure.DevOps.ServiceConnections.ProjectValidUsers
- Azure.DevOps.ServiceConnections.Scope
- Azure.DevOps.ServiceConnections.WorkloadIdentityFederation
- Azure.DevOps.Tasks.VariableGroup.Description
- Azure.DevOps.Tasks.VariableGroup.InheritedPermissions
- Azure.DevOps.Tasks.VariableGroup.NoKeyVaultNoSecrets
- Azure.DevOps.Tasks.VariableGroup.NoPlainTextSecrets
- Azure.DevOps.Tasks.VariableGroup.ProjectValidUsers
This project welcomes contributions and suggestions. Please read CONTRIBUTING.md for details on how to contribute.
This project is licensed under the MIT License.
- Bernie White for creating PSRule.
- PSRule
- PsrAzDo-workbooks - Azure Monitor Workbooks for PSRule.Rules.AzureDevOps
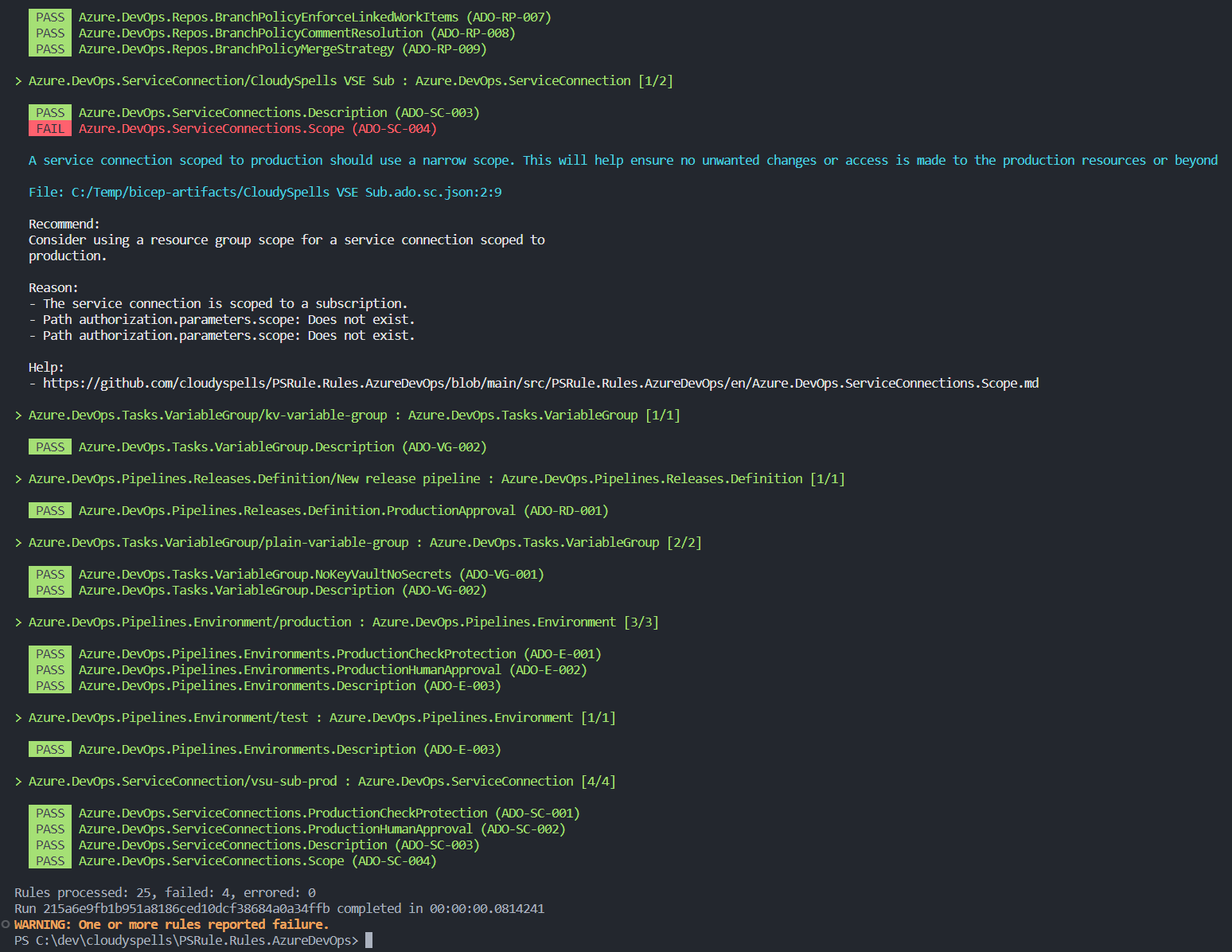
- Auditing an Azure DevOps project configuration with PSRule
- Audit Azure DevOps configuration with Sarif scan reports from the pipeline
- Azure DevOps Security best practices