✨ The Kubernetes Goat is designed to be an intentionally vulnerable cluster environment to learn and practice Kubernetes security 🚀
🙌 Refer to https://madhuakula.com/kubernetes-goat for the guide 📖
-
Ensure you have admin access to the Kubernetes cluster and installed
kubectl. Refer to the docs for installation -
Ensure you have the
helmpackage manager installed. Refer to the docs for installation -
To set up the Kubernetes Goat resources in your cluster, run the following commands:
git clone https://github.com/madhuakula/kubernetes-goat.git
cd kubernetes-goat
chmod +x setup-kubernetes-goat.sh
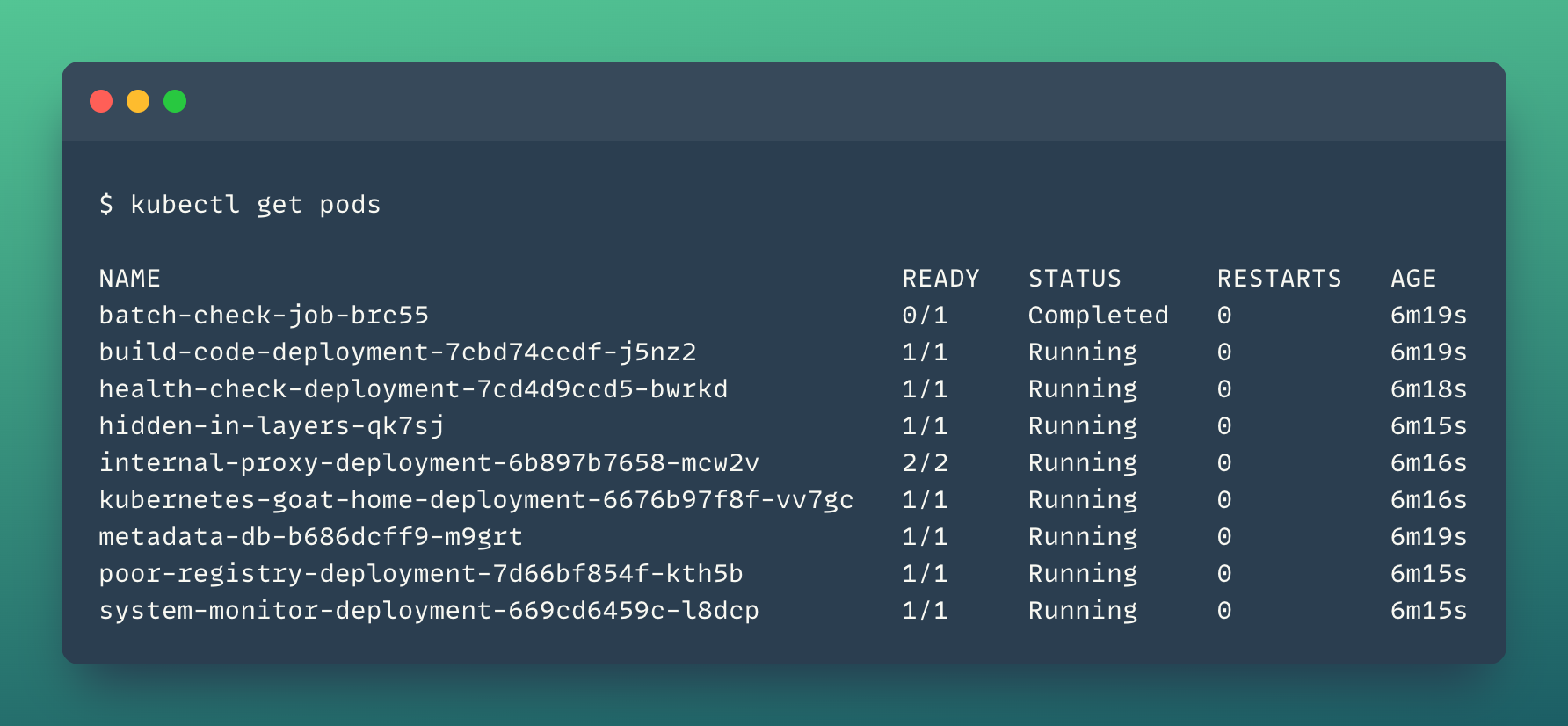
bash setup-kubernetes-goat.sh- Ensure the pods are running before running the access script
kubectl get pods- Access Kubernetes Goat by exposing the resources to the local system (port-forward) by the following command:
bash access-kubernetes-goat.sh- Then navigate to
https://127.0.0.1:1234
Refer to https://madhuakula.com/kubernetes-goat/docs/how-to-run for setting up Kubernetes Goat in various environments like GKE, EKS, AKS, K3S, KIND, etc.
- Sensitive keys in codebases
- DIND (docker-in-docker) exploitation
- SSRF in the Kubernetes (K8S) world
- Container escape to the host system
- Docker CIS benchmarks analysis
- Kubernetes CIS benchmarks analysis
- Attacking private registry
- NodePort exposed services
- Helm v2 tiller to PwN the cluster - [Deprecated]
- Analyzing crypto miner container
- Kubernetes namespaces bypass
- Gaining environment information
- DoS the Memory/CPU resources
- Hacker container preview
- Hidden in layers
- RBAC least privileges misconfiguration
- KubeAudit - Audit Kubernetes clusters
- Falco - Runtime security monitoring & detection
- Popeye - A Kubernetes cluster sanitizer
- Secure network boundaries using NSP
- Cilium Tetragon - eBPF-based Security Observability and Runtime Enforcement
- Securing Kubernetes Clusters using Kyverno Policy Engine
Here is the detailed step by step guide for learning and using Kubernetes Goat 🎉: documentation guide
Reference: https://madhuakula.com/kubernetes-goat
Kubernetes Goat has intentionally created vulnerabilities, applications, and configurations to attack and gain access to your cluster and workloads. Please DO NOT run this alongside your production environments and infrastructure. We highly recommend running this in a safe and isolated (contained) environment.
Kubernetes Goat is used for educational purposes only. Do not test or apply these attacks on any systems without permission. Kubernetes Goat comes with absolutely no warranties, by using it you take full responsibility for all outcomes.
Thanks to to these wonderful people: 🎉