Creates a Chef Complianc Web server in a Public Subnet with Internet Gatewayy attached on an existing VPC.
It then attaches an EIP and finally adds the instance to an existing instance-to-instance security group.
VPC
Public Subnet, IGW, Private Subnet/s.
Either use an existing VPC Infrastructure or you can use the following VPC Template to create a one.
Available EIP
us-west-2
us-east-1
EC2 Instance
EIP
IAM Role
IAM Instance Profile
Security Group
Launch
us-west-2
us-east-1
View in Designer
How To Video
COMING SOON
AWS CLI Example
aws cloudformation create-stack --profile {AWS Profile Name} --stack-name {Stack Name} --capabilities CAPABILITY_IAM --template-url "https://s3.amazonaws.com/stelligent-public/cloudformation-templates/github/labs/chef_compliance/chef-compliance.template"
--parameters file:https:///localpath/to/custom-parameters.json
Option 2 - Pass Parameters on CLI
--parameters ... COMING SOON
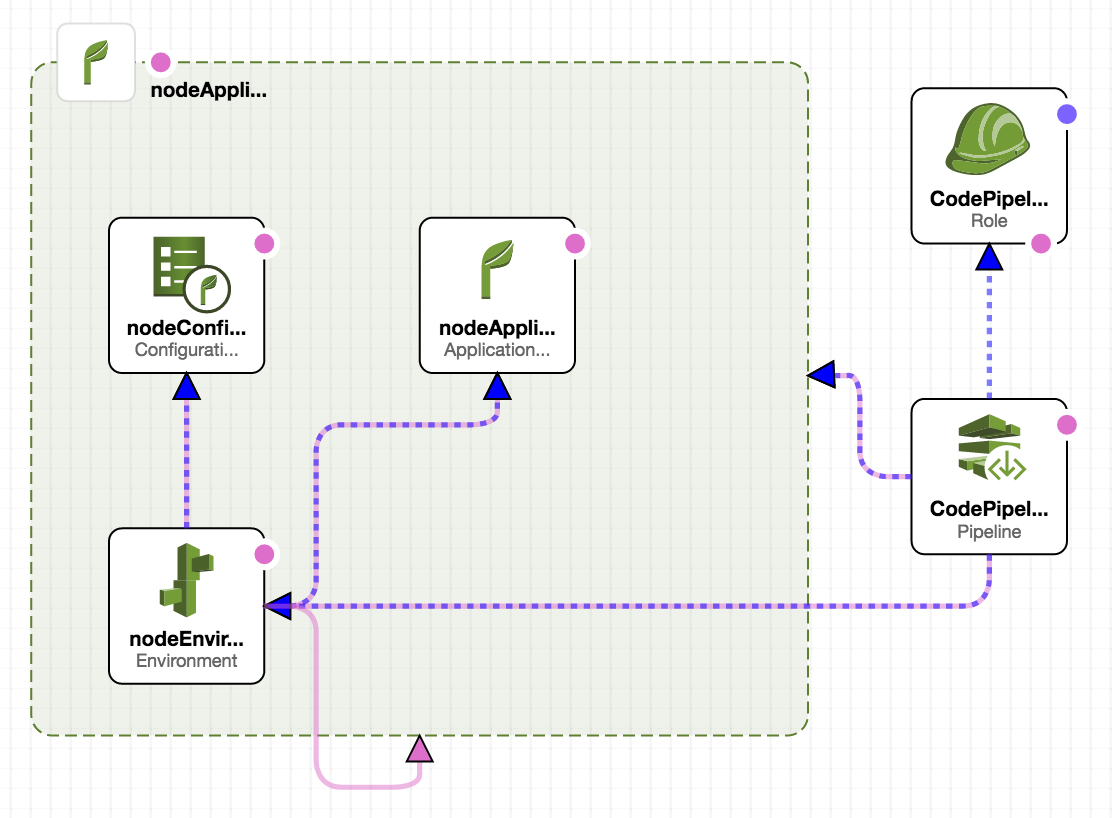
Automates the integration between AWS Elastic Beanstalk and CodePipeline
CodeCommit Repo
us-east-1
IAM InstanceProfile, Policy, and Roles
Elastic Beanstalk - ConfigurationTemplate, Environment
CodePipeline with CodeCommit Integration
Launch
us-east-1
View in Designer
How To Video
COMING SOON
AWS CLI Example
aws cloudformation create-stack --profile {AWS Profile Name} --stack-name {Stack Name} --capabilities CAPABILITY_IAM --template-url "https://s3.amazonaws.com/stelligent-public/cloudformation-templates/github/labs/eb/elasticbeanstalk-codepipeline.json"
--parameters file:https:///localpath/to/custom-parameters.json
Option 2 - Pass Parameters on CLI
--parameters ParameterKey=RepositoryName,ParameterValue=codecommit-demo"
Automates the integration between AWS CodeCommit and CodePipeline
EC2 Key Pair
CodeCommit Repo
us-east-1
IAM InstanceProfile, Policy, and Roles
EC2 Instance for CodeDeploy
CodeDeploy
CodePipeline with CodeCommit Integration
Launch
us-east-1
View in Designer
How To Video
COMING SOON
AWS CLI Example
aws cloudformation create-stack --profile {AWS Profile Name} --stack-name {Stack Name} --capabilities CAPABILITY_IAM --template-url "https://s3.amazonaws.com/stelligent-public/cloudformation-templates/github/labs/codecommit/codepipeline-codecommit.json"
--parameters file:https:///localpath/to/custom-parameters.json
Option 2 - Pass Parameters on CLI
--parameters ParameterKey=EC2KeyPairName,ParameterValue=stelligent-dev"
Automates the integration between AWS OpsWorks, CodeCommit and CodePipeline
EC2 Key Pair
us-east-1
IAM InstanceProfile, Policy, and Roles
SecurityGroupIngress and SecurityGroup
OpsWorks Stack, Layer, App and Instance
CodePipeline
Launch
us-east-1
View in Designer
How To Video
COMING SOON
AWS CLI Example
aws cloudformation create-stack --profile {AWS Profile Name} --stack-name {Stack Name} --capabilities CAPABILITY_IAM --template-url "https://s3.amazonaws.com/stelligent-public/cloudformation-templates/github/labs/opsworks/codepipeline-opsworks.json"
--parameters file:https:///localpath/to/custom-parameters.json
Option 2 - Pass Parameters on CLI
--parameters ParameterKey=KeyName,ParameterValue=stelligent-dev"
Creates three test instances in an existing VPC. Each instance is a different operating system. They are; Red Hat Enterprise Linux 7, Ubuntu 14 and Windows 2012 R2.
3 EC2 Instances
IAM Role
IAM Instance Profile
Launch
us-west-2
us-east-1
View in Designer
How To Video
COMING SOON
AWS CLI Example
aws cloudformation create-stack --profile {AWS Profile Name} --stack-name {Stack Name} --capabilities CAPABILITY_IAM --template-url "https://s3.amazonaws.com/stelligent-public/cloudformation-templates/github/labs/test_instances/rhel-ubuntu-win2012.template"
--parameters file:https:///localpath/to/custom-parameters.json
Option 2 - Pass Parameters on CLI
--parameters ... COMING SOON