An IDAPython script for IDA Pro that helps reverse engineer binaries that are using the OPC Data Access protocol.
It can be used to analyse such malware families as Havex RAT and Win32/Industroyer.
The script identifies CLSID, IID, and LIBID constants and creates structures and enumerations. Afterwards, these structures can be used to annotate COM method call parameters.
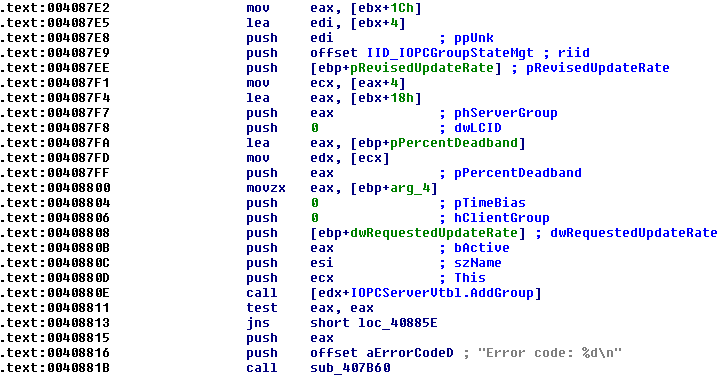
Example: